Abstract
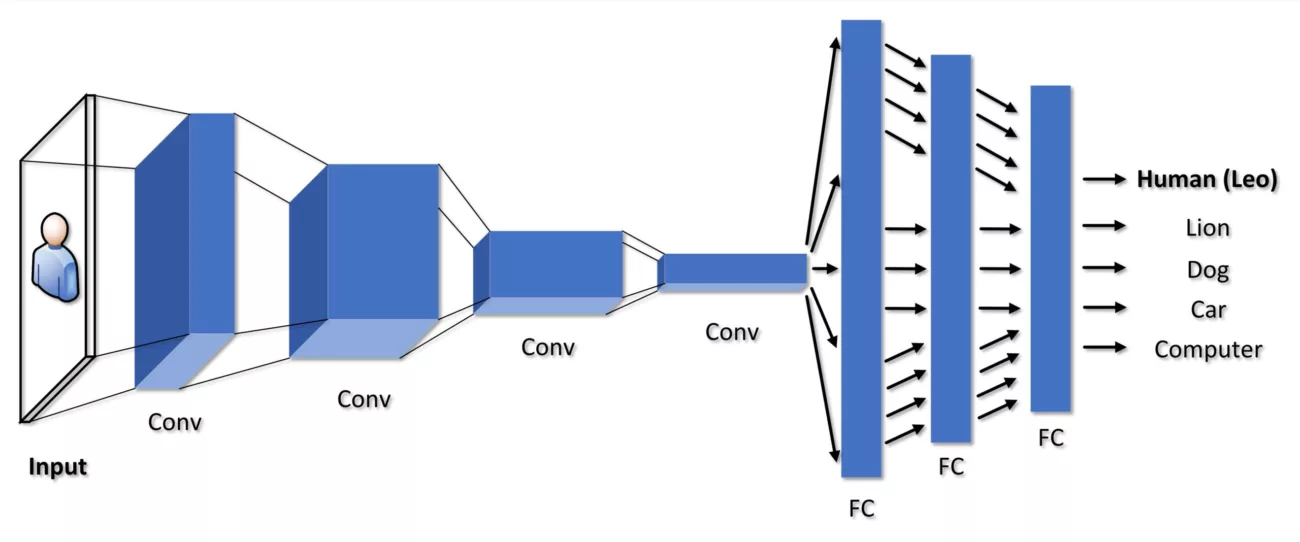
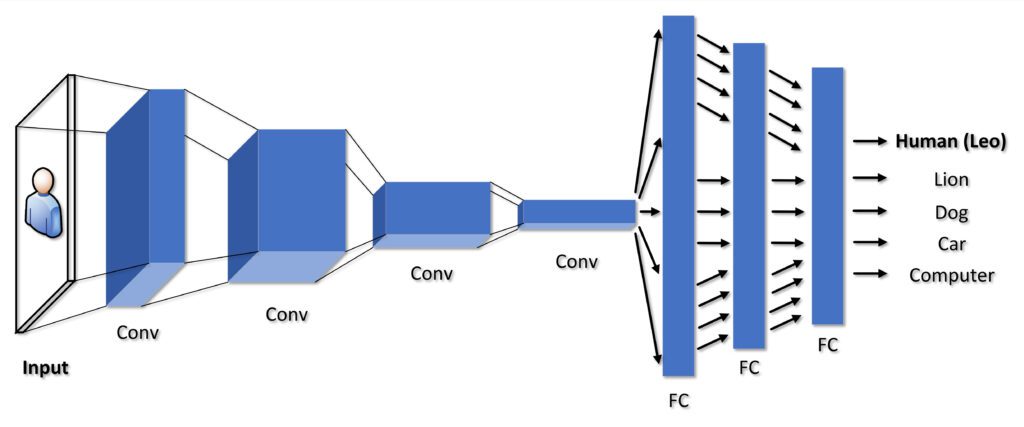
This research focuses on Windows Portable Executable (PE) packed malware detection and Deep Learning (DL) using the Convolutional Neural Network (CNN) algorithm. Our primary goal is to improve the usage of DL techniques in Cybersecurity to strengthen the defenses against cyberattacks on U.S. Department of Defense (DoD) systems. According to our hypothesis, existing Cross Domain Solutions (CDSs) can be upgraded to include built-in DL-CNN algorithms for identifying well-crafted packed malware. To put this into perspective, implementing DL-CNN into the Cross Domain Solution (CDS) filter software will significantly enhance the effectiveness and detection of packed malware. CDSs are strategically positioned between unclassified and classified systems, and with DL-CNN capabilities, the CDS virus detection filter will learn to detect malware on its own, regardless of whether the malware is well-crafted, packed, or encrypted. Using our trained deep neural network model, we were able to identify Windows packed PE malicious executables from Windows packed PE benign executables with an average training accuracy of 94 percent and a validation accuracy of 93 percent. Although the DL-CNN algorithm’s results could be enhanced through further development and refinement using KerasTuner, this research provides a solid foundation. Our experiments were conducted on our lab computer system and in the Amazon SageMaker Studio Lab and Google Collab cloud environments.
International Conference on Data Science and Its Applications (ICoDSA), July 6-7, 2022, Bandung, Indonesia
The full paper can be accessed here:https://doi.org/10.1109/ICoDSA55874.2022.9862936
33 Technologies specializes in cloud solutions and can assist you in evaluating your current IT infrastructure, identifying your cloud requirements, and developing a comprehensive plan. In addition to data migration, user training, and ongoing cloud management and monitoring, our team of experts can also assist with data migration.
Contact us today to learn how we can help you migrate to the cloud and reap the benefits of increased security, efficiency, and cost savings.
Affiliate links generate a commission for our business. The author’s opinions and evaluations are not influenced by commissions. This post does not represent official United States Department of Defense policy, funding, or endorsement.